Surfing the web, I have found a nice article about BGP weakness. This document, entitled “Defending Against BGP Man-In-The-Middle Attacks“, was presented by Earl Zmijewski during Black Hat DC 2009 (Hyatt Regency Crystal City – February 16-17 – Arlington, Virginia).
The slides focus on four points:
- BGP Routing Basics – Enough to understand and identify the threat
- BGP Update Messages
- BGP Attributes
- Some real examples
- The Man-In-The-Middle Attack:
- How BGP MiTM attack work
- What are the techniques used by an attacker to “tune” the attack (Obscuring the MITM attack with TTL adjustment)
- Detecting the Attack – Methods for observing the attack in the wild:
- Traceroute
- Latency
- BGP Alarming Services (BGPmon, IAR, …)
- Case Studies – Analyzing historical data for attack evidence
“At DEFCON 16, Alex Pilosov and Tony Kapela presented a new BGP attack in which traffic to a victim is hijacked, but then transparently routed to the intended recipient. This allows for wholesale eavesdropping, including alteration, of all incoming traffic to the victim. In this talk, we review enough BGP routing background to understand the threat and how it breaks the trust model inherent in Internet routing.
Then we review possible detection mechanisms via data aggregation from global route collection. The tip-off to such attacks includes prefix de-aggregation, invalid originations, invalid AS adjacencies, and even improbable AS paths. Detection techniques depend whether or not you know ground truth, i.e., if you are looking to defend your own network or simply observe such hijacks in the wild.
We conclude with case studies of applying these techniques to global routing data.”
BGP MiTM attack
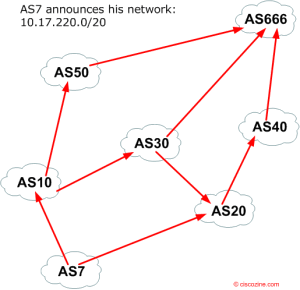
1) Normal BGP behavior: AS7 announces his network to the other autonomous system
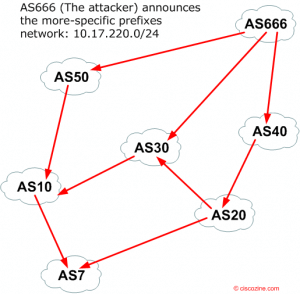
2) The attacker (AS #666) announces the more-specific prefixes network
… In BGP, most specific route to an IP address wins and the traffic is sent to AS666 instead of AS7!!!
References:

Good presentation. However, the video appears to have gone missing:
http://media.blackhat.com/bh-dc-09/video/Hepner/BlackHat_DC_2009_Hepner_Zmijewski_Defending_BGP.m4v
Check this out http://www.renesys.com/wp-content/uploads/2013/05/blackhat-09.pdf